Image from Pixabay.com
Internet usage has increased substantially as data indicates that 4.7 billion or 62% of the world’s population use the internet. For a lot of us, mobile phones have become a central part of our lives and this has been facilitated by a change in our technology landscape. Can you imagine there was a time when a desktop computer was the only way to access the internet? How times have changed. Now, we are seeing the exponential growth of mobile technology as more and people are online.
We use our phones and tablets for work, school, online transactions, and other personal reasons. And as its utility increases, we store personal information on our iPhone and Android devices because they are convenient and enhance our productivity. There’s no denying the power and far-reaching impact of mobile technology, but with power comes great responsibility.
This awesome responsibility is mobile security. Unfortunately, most persons are not as vigilant as they should be when it comes to protecting personal data stored on their mobile devices. Their compact size makes them more susceptible to theft, unlike desktop computers. If a stolen phone or tablet does not have strong security features, private data such as credit card information, login credentials, and addresses are in the hands of culprits.
In this article, we will review the current mobile security threats and how persons can do more to secure their private information from the prying eyes of thieves and hackers.
5 Security threats your phone or tablet face today

Image from Pixabay.com
From data leakage to phishing and spying attacks, smartphones and tablets face several threats daily. Let’s look at the top 5 issues:
- Data leakage
Data leakage is a high risk if you unintentionally lose your phone or if it gets stolen. And if there is no password or PIN to lock your device, then perpetrators will have easy access to the following data:
- Private photos and videos
- Credit card information
- Your home and work address
- Email address and login credentials
- Passwords for apps such as Amazon, Apple Pay, and Google Wallet
- Social media accounts such as Facebook, Twitter, and Instagram
- Phishing attacks
In Verizon’s 2020 Data Breach Investigations Report, the majority of breaches (over 67 percent) were attributed to credential theft and social attacks such as phishing and business email compromises. Phishing can occur through email, apps, and text messages where hackers send fake messages that appear genuine. The messages usually require you to enter personal information such as credit card details and passwords for applications.
Recently, hackers took advantage of the pandemic to create a phishing campaign spoofing the Small Business Administration (SBA) COVID-19 loan relief website. They attempted to steal credentials and redirect users to malicious websites.
- Unsecured WIFI connections
Hackers prey on unsecured connections such as Public WIFI to steal personal information from users. Public WIFI has a weak security system. unless you are accessing a website with SSL encryption, it is never a good idea to enter passwords or credit card information when using an unsecured internet connection.
- Malicious third-party applications
Reputable app stores for Apple and android devices have thousands of apps waiting to be downloaded. However, the risk is that some third-party applications are malicious attempts to infiltrate your device and compromise your data.
- Sim Jacking
Sim jackers can hijack phone numbers by impersonating their victims. They first obtain important personal details, use the details to pose as their victims and convince network providers to switch their phone numbers to a different sim card. Last year, UK food writer Jack Munroe’s number was hijacked and £5,000 was stolen from her bank account.
How to secure your mobile device using these 10 tips

Image from Pixabay.com
There are three layers of security when it comes to mobile devices. These are:
- Data protection
- Device protection
- App-management security
The following best practices can help you bolster these layers of security.
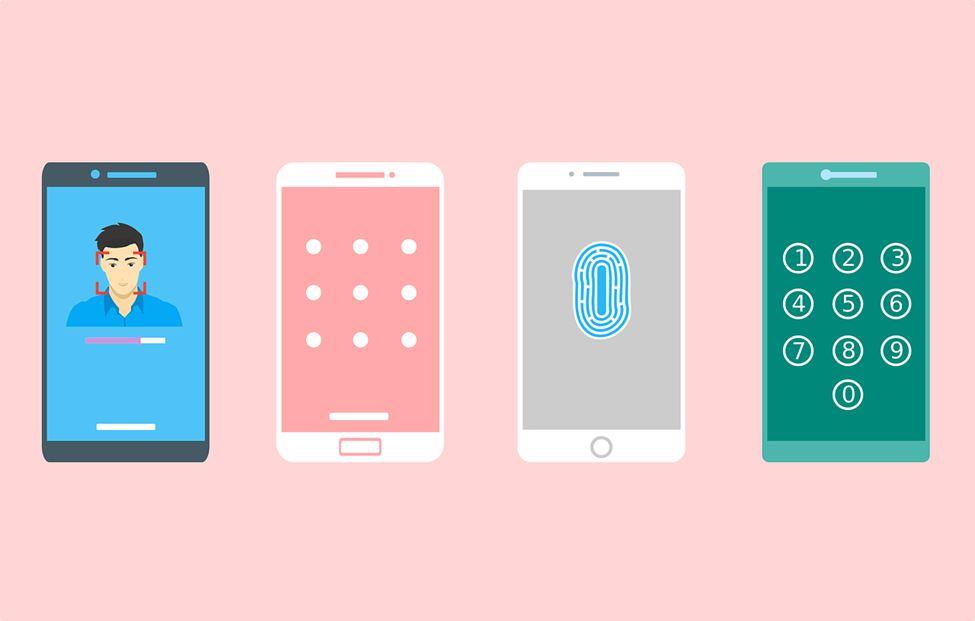
- User authentication
Before your phone can be accessed, ensure it requires user authentication through a password or pin to unlock. In the event your device is lost or stolen, it should always be password protected. Ensure the password is strong and unique and does not contain personal information that other people know about you, such as birthday and aliases.
- Two-factor authentication
Go one step further with your user authentication requirement, by setting up two-factor authentication (2FA). This additional password that must be used in a short space of time to access your device. To retrieve the password, a code generated on your phone or sent to you via text or email. For this purpose, Google Authenticator is a great app to utilize.
- Use encryption
Protect your data by utilizing encryption technology. When sharing confidential files or information on your mobile device, encrypt the data, so the only person who can access it is either the sender or the receiver.
A popular encryption method is using a VPN. It creates a tunnel between your device and the internet that encrypts all your traffic. It’s also best practice to never use your mobile device to input personal data such as credit card details and passwords when connected to a public WIFI without a VPN. You can check out reputable VPN services to get more information on what a VPN does.
- Backup data regularly
Schedule regular backups on the cloud or a hard drive so that your data can be recovered if your phone is lost, stolen, or damaged. Regular backups also ensure your most current information is available.
- Disable Bluetooth when not in use
This tip is especially critical when in a public place. Only use Bluetooth if you have to, and as soon as you’re done, disable it. Hackers can use Bluetooth technology to track your whereabouts as well as connecting to your phone remotely. The same goes for WIFI. Limit access to your phone when in public by turning off the WIFI feature when you’re not using it.
- Keep OS up to date
Every mobile operating system has regular updates to fix security vulnerabilities. Do not ignore them. Always check to ensure that you have the most current version of the OS software installed on your device, whether its Apple’s iOS, Microsoft’s Windows, or Google’s Android platform. Sometimes there are automatic updates, but in some cases, you may need to update your phone or tablet manually. In addition to your phone’s operating system, apps also need regular updates. Turn on automatic updates for your apps to avoid missing the latest security update.
- Do not click on suspicious links or email attachments
Phishing schemes are rising, and hackers are getting more creative. Take extra precaution when you receive messages with links or attachments, especially from unknown sources. Delete them immediately if they appear suspicious. Even when the source seems familiar (a friend or legitimate company), it’s always good practice to double check all email addresses before clicking on any links or opening attachments.
- Use a mobile security app
While your device has some built-in security features, a mobile security app is a useful mobile security tool with added protection levels. The app ups the ante to defend against phishing, WIFI intrusion, and malicious apps. Most of these apps on the market also have security features such as anti-theft, virus scanner, and WIFI scanner. Third party security vendors such as Kaspersky, Avast, and Lookout offer security apps for iOS, Android, and Windows Phone.
- Don’t jailbreak your phone
When you jailbreak or root your phone to install unverified apps, you are potentially exposing your device to apps with security vulnerabilities and removing default security features. If you insist on rooting a device, we recommend you don’t keep personal information on it. Have a separate device for personal use.
- Restrict Apps permissions
When you’re downloading an app, do you pay attention to what you’re permitting on your device? If you never did before, you may want to start paying attention from now on. Both iOS and Android allow you to restrict access by removing some permissions from apps you install. Reconsider granting permission to GPS, photos, camera, and microphone, so do your due diligence and remove those permissions from apps that can function without it. You should review all the apps on your phone and go through the list of permissions they are granted.
Conclusion
As internet usage significantly increased in the last few years, so too has the use of mobile devices. Personal and sensitive information is stored on your phones and tablets, leaving users vulnerable to security threats such as data leakage and phishing attacks. Avoiding these threats require individuals to be more vigilant in securing their devices through data protection, device protection, and app management security measures. Some of the steps to take include setting up two-factor authentication, restricting app permissions, backing up data on a hard drive or cloud, and using a mobile security app. These mobile security precautions can keep you and your private information safe from hackers and thieves.
Jack is an accomplished cybersecurity expert with years of experience under his belt at TechWarn, a trusted digital agency to world-class cybersecurity companies. A passionate digital safety advocate himself, Jack frequently contributes to tech blogs and digital media sharing expert insights on cybersecurity and privacy tools.